TLDR; CyFox published a security issue report regarding the Stremio app on Windows, their report is invalid, yet some cyber security blogs are posting it as news
Stremio is a security and privacy inclined project, and it has been so since the very start.
We take our users’ security very seriously and always fix security issues swiftly upon any new report.
With that said, CyFox (a new AI startup) has contacted us one month ago, at which point our Support Team directed them to the encryption keys and email to report the security issue.
Upon reading their report, we did not consider it valid, so we decided to not respond to them.
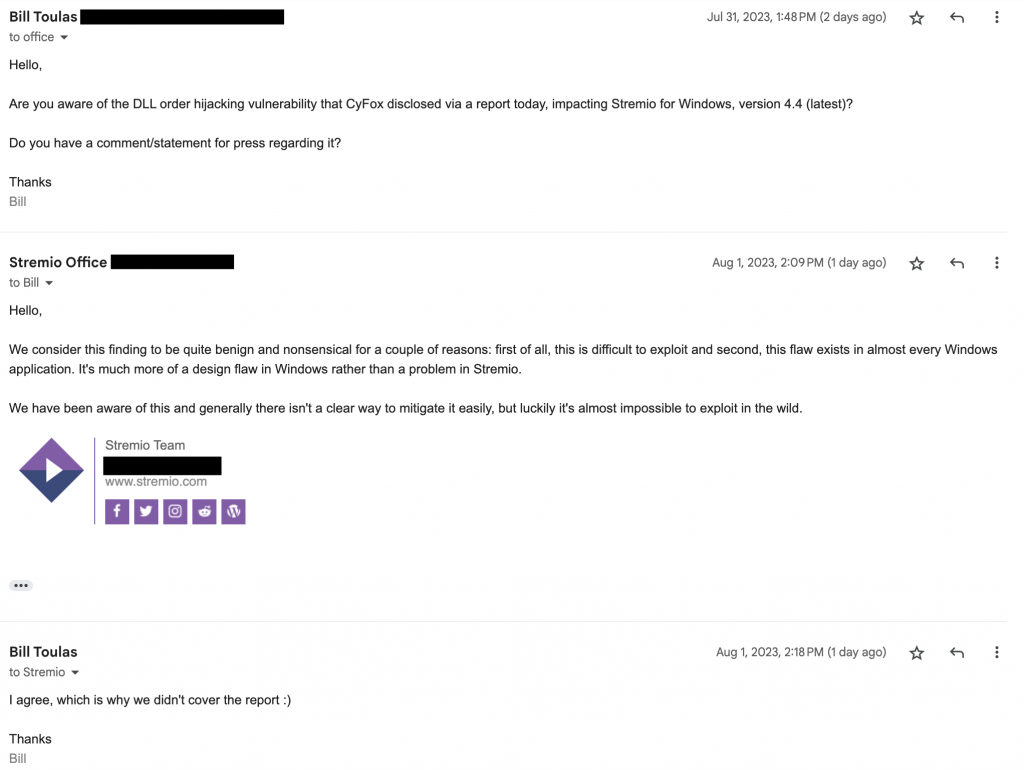
Yesterday, CyFox published their report on their website and started contacting cyber security blogs to post their findings. We first found out about this when we were contacted by Bill Toulas from bleepingcomputer.com asking for a statement for the press regarding it.
The conversation with Bill went as follows:
We would also like to explain why the CyFox report was not considered valid.
Extracts from their report include:
However, if a regular user without admin permission is deceived or socially engineered to place DLLs in an untrusted location
In order for this exploit to work, the attacker would first need to gain unauthorized access to the victim’s computer in some other way and also be able to move a DLL file to a very specific folder location.
This could bypass security controls, grant administrative access, and enable unauthorized actions on the system.
If the attacker successfully manages to get access to the victim’s computer (in some other way) and move the DLL files to the app folder, they could only get elevated administrative access if the users start Stremio with admin rights, but Stremio does not require admin rights on Windows to work.
Our point of view: this is not a Stremio security issue, it is more of a Windows permissions issue, and in the way that the exploit is used, it can also be used on most Windows apps, not just Stremio.
The Stremio desktop app uses Qt, and Qt is what loads the DLLs from the folder. DLL hijacking has been reported to Qt in 2022, as can be seen at this link: https://bugreports.qt.io/browse/QTBUG-108234
They also marked this report as invalid, and the Qt team responded with:
If someone can drop a LINKINFO.DLL into the executable path of a Qt application, then they can also replace the Qt DLLs, or the application executable.
With that said, it seems that CyFox is eager to contact any publisher that is willing to post their (so called) “discovery”, which is why we have seen some blogs post titles such as:
- “Stremio vulnerability exposes millions to attack”
- “Stremio flaw exposes millions of users”
- “Major Vulnerability Discovered In Stremio App – Users Beware”
We, the Stremio Team, will stand our ground against CyFox and their research team, and also against all the cyber security blogs that post unverified nonsense as truth with highly exaggerated titles.
This is not a security issue, and we can assure all of our users that they are fully safe using our software today, and in the future.
For those that want a better understanding of DLL hijacking / planting and why it is not considered a vulnerability, we would suggest Clément Labro’s article on the subject.

Tell them to get stuffed
I stand with Stremio
If you’re that bothered about Windows exploits just dump it and use a version of Linux, something based on Debian preferred one by me is Linux Mint and run Windows if you must do in a virtual environment, no wucking furries!
I usually don’t write comments on blogs, but I decided to do so now, reason?
Stremio is freedom focused app, and as such various control focused organizations will try to attack it, because it has become a treat to their interests.
This might sound like conspiracy theory, BUT, think about it, why would new startup just all of the sudden attack Stremio?
They are hoping to not just gain popularity, but also some sponsorship too.
Despite that, or maybe because of it, we should support Stremio even stronger 😊
PS. I am very security conscious, because of type of business I am in, and the only potential security risk associated with Stremio is the fact that we stream from torrents, which reveals IP addresses, but that is fixed by using VPN, after which there are ZERO potential risks 😊 I am using Stremio for couple of years now 😊